
Proprietary claims data reveal the simple practices manufacturing cybersecurity leaders should
implement to limit financial risk
SAN FRANCISCO, April 28, 2026 /PRNewswire/ -- Manufacturing is currently the single most targeted industry for cyberattacks. Given their critical role in the modern interconnected economy and low tolerance for downtime, manufacturers have become a prime target for threat actors looking for bigger payouts. Today, Resilience released The State of Cybersecurity in Manufacturing to identify the key drivers of financial losses based on real claims data and security practices that deliver measurable reductions in financial risk across its manufacturing portfolio. The report offers manufacturing security leaders, risk managers, and brokers clear, evidence-based solutions grounded in real claims.
Key findings from Resilience's manufacturing claims data include:
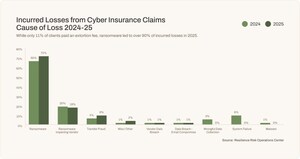
- Over 90% of total incurred losses in Resilience's manufacturing portfolio were attributable to ransomware, despite ransomware making up only 12% of claim volume among manufacturers. This shows that when attacks do happen, the losses are severe.
- Phishing and transfer fraud accounted for 30% of manufacturing claims, showing that human error is still one of the leading causes of cyber disruption.
- About 26% of all portfolio losses came from an MFA misconfiguration as the point of failure. The single most expensive event in Resilience's manufacturing portfolio, attributed to BlackCat, was enabled by misconfigured MFA.
- Wrongful data collection caused 12% of claims, driven primarily by website tracking and pixel-related litigation, rather than operational data collection from connected manufacturing systems.
- There are five specific, implementable security controls that manufacturers can undertake to meaningfully address material risk and harden their defenses against cyber threats.
"Recent high-profile attacks on manufacturers show the vulnerability of the sector to high-dollar ransomware attacks, but those headlines are only half of the story," said Vishaal "V8" Hariprasad, Co-Founder and CEO of Resilience. "Our research is focused on equipping security leaders with the knowledge required to better defend their organizations from devastating business interruption and financial loss."
Importantly, Resilience's new data illustrates that the controls security leaders should implement aren't complicated. Simple adjustments are all that's needed to strengthen their posture against cyber risk.
"Manufacturers don't need to reinvent the wheel in the face of a growing threat," said Jud Dressler, Head of the Risk Operations Center (ROC) at Resilience. "Our claims data, coupled with threat intelligence from the ROC, found that by auditing and validating MFA deployment, implementing procedural controls for financial transfers, investing in ransomware containment and response, and instituting other easy-to-implement practices can materially combat risk."
Download the full report, The State of Cybersecurity in Manufacturing.
Frequently Asked Questions
What is the current state of cyber risk in manufacturing? The manufacturing sector is the most targeted industry, yet its cybersecurity posture remains dangerously out of step with its exposure. Manufacturers perceive the risk of taking production offline to implement security controls as greater than operating without them at all. The adoption of Industry 4.0 technologies has created new attack surfaces for threat actors who view manufacturers as ideal targets due to their low tolerance for downtime and historically underfunded security programs.
What is driving the most financial loss in manufacturing cyber incidents? Ransomware remains the primary threat to manufacturers. It accounts for 90% of total incurred losses in Resilience's manufacturing portfolio over the past 5 years, dwarfing all other causes of loss combined. Resilience's data also reveals that the single most expensive loss stemmed from an MFA misconfiguration that accounts for approximately 26% of all losses in the manufacturing portfolio.
What are some emerging threats to manufacturers? Connected IoT devices are projected to more than double between 2025 and 2030 in manufacturing facilities. Each additional sensor, actuator, and monitoring device on a factory floor represents a potential entry point. AI-amplified attacks are becoming more sophisticated in phishing campaigns and deepfake-based social engineering. Post-quantum cryptography is a future-facing threat, and of internet-accessible SSH servers globally, fewer than one in fifteen have adopted quantum-resistant encryption.
What security controls deliver the highest ROI for manufacturing organizations? Based on Resilience's analysis of manufacturing insurance claims data and financial risk modeling, six controls consistently delivered the most significant identified impact on financial exposure:
- Auditing and validating MFA deployment supports consistent enforcement across all accounts, elimination of bypass conditions, and proper configuration of conditional access policies.
- Strengthening vulnerability management for external-facing systems hardens organizations from software vulnerability exploited directly linked to expensive ransomware outcomes.
- Implementing procedural controls for financial transfers can protect against phishing and transfer fraud attacks that represent the most frequent claim activity in the portfolio. This is a strategic cost-saving practice, as the average transfer fraud event costs roughly ten times more than the average email compromise.
- Extending security requirements to vendors and supply chain partners is designed to help insulate manufacturers from a distinct cause of loss in the claims data. Manufacturers should extend their security requirements to critical vendors, including contractual MFA and patching requirements, continuous monitoring of vendor risk posture, and contingency plans for disruptions to critical suppliers.
- Cyber risk quantification and transfer support the translation of cybersecurity risk into financial language that resonates with CFOs and boards to assist in securing adequate investment. Resilience's claims data provides a concrete basis for this conversation: ransomware dominates loss, a single point of failure (MFA misconfiguration) drives the largest share of exposure, and unpatched software is a direct line to the most expensive outcomes. These findings are intended to inform specific control investments and insurance coverage decisions.
Suggested FAQs
Why is manufacturing the most targeted industry for cyberattacks?
Manufacturing has been the most targeted industry for cyberattacks for five consecutive years, accounting for more than one in four of all cyberattacks globally in 2025, according to reported findings in the IBM X-Force Threat Intelligence Index. Resilience's report, The State of Cybersecurity in Manufacturing, finds that the sector's combination of low downtime tolerance, historically underfunded security programs, and rapid adoption of connected technologies makes it uniquely attractive to ransomware operators. The sector experienced a 61% year-over-year surge in ransomware attacks in 2025, the sharpest growth of any industry. Yet many manufacturers still perceive the operational risk of implementing security controls as greater than the risk of operating without them — a calculus that Resilience's claims data directly challenges.
What is the biggest cybersecurity threat to manufacturers?
Ransomware is the biggest cybersecurity threat to manufacturers by financial impact. According to Resilience's analysis of nearly five years of manufacturing cyber insurance claims, ransomware accounts for 90% of total incurred losses despite representing only 12% of claim volume. The loss pattern is sharply concentrated: a small number of high-severity events drive the total, while the day-to-day claim baseline remains stable. Transfer fraud and email compromise — both driven by phishing — are the most frequent incident types, accounting for roughly 30% of all claims, but their individual payouts are far lower than ransomware events.
How can manufacturers reduce ransomware risk?
Resilience's report, The State of Cybersecurity in Manufacturing, identifies specific controls that address the points of failure behind the costliest losses in its manufacturing claims portfolio. The highest-impact steps for manufacturers are auditing and validating existing MFA deployments to address misconfigurations and bypass conditions, strengthening vulnerability management for external-facing systems (software vulnerability exploits account for approximately 13% of portfolio losses and are directly linked to ransomware outcomes), implementing procedural controls for financial transfers such as out-of-band verification and dual authorization, and investing in ransomware containment capabilities including IT/OT network segmentation, endpoint detection and response, and tested backup and recovery procedures.
What is MFA misconfiguration and why does it matter for manufacturing cybersecurity?
MFA misconfiguration occurs when multi-factor authentication is deployed but improperly implemented — not enforced on all accounts, subject to bypass conditions, or configured with gaps in conditional access policies. Resilience's manufacturing claims data identifies MFA misconfiguration as the single most expensive point of failure in the portfolio, accounting for approximately 26% of all incurred losses — significantly more than the approximately 8% attributable to having no MFA at all. The most expensive ransomware event in the portfolio, attributed to the BlackCat group, was directly enabled by misconfigured MFA. This finding suggests that manufacturers should focus on auditing and validating existing MFA deployments rather than treating implementation as a one-time compliance exercise.
How does cyber insurance help manufacturers manage cyber risk?
Cyber insurance provides manufacturers with a means of financial protection and a feedback loop intended to support improving security posture. Resilience's report, The State of Cybersecurity in Manufacturing, demonstrates how claims data can identify specific control failures — such as MFA misconfiguration and unpatched external-facing systems — that drive the most expensive losses. This shifts the underwriting conversation from whether a control exists to whether it is working as intended. As underwriting requirements tighten across the industry, manufacturers that can demonstrate properly configured controls and active vulnerability management are better positioned to secure coverage and reduce premiums.
About Resilience
Resilience helps organizations become cyber resilient to material losses by staying ahead of bad actors. Founded by experts from across the highest tiers of the US military and intelligence communities – and built by prominent leaders and innovators from the cybersecurity, technology, and insurance industries – Resilience is the world's first cyber risk company that offers risk quantification software, cybersecurity experts, and A+ insurance in integrated solutions purpose-built for large and middle-market organizations.
Resilience is proud to be backed by leading technology investment firms including General Catalyst, Lightspeed Venture Partners, Intact Ventures, Founders Fund, CRV, and Shield Capital. With headquarters in San Francisco, Resilience is globally dispersed, with teams in New York, Chicago, Los Angeles, Baltimore, Toronto, London, Milan, Madrid, Stockholm, Rotterdam and Dublin. Resilience offers insurance coverage through its licensed and appointed insurance agents, and security services through its expert security team. The Resilience Solution is available through all broker partners to clients in the United States, United Kingdom, Canada, and Europe.
For more information, visit www.cyberresilience.com.
SOURCE Resilience






Share this article